The deluge of cyberattacks sweeping across the world has governments and companies thinking about new ways to protect their digital systems, and the corporate and state secrets stored within. For a long time, cybersecurity experts have erected firewalls to keep out unwanted traffic and set up decoy targets on their networks to distract hackers who do get in. They have also scoured the internet for hints about what cybercriminals might be up to next to better protect themselves and their clients.
Search Results: facebook (1311)
Of all the fictional virtual assistants we know from pop culture, few stand up to the original and perhaps most famous: the HAL 9000 from the 1968 Stanley Kubrick film 2001: A Space Odyssey.
We should probably be thankful for that. After all, Alexa may shut your lights off, but she won’t turn against you and wreak havoc on your life. Or will she?
Though it’s not exactly unexpected, it’s nonetheless still a pity — Netflix has officially canned its last two Marvel offerings.…
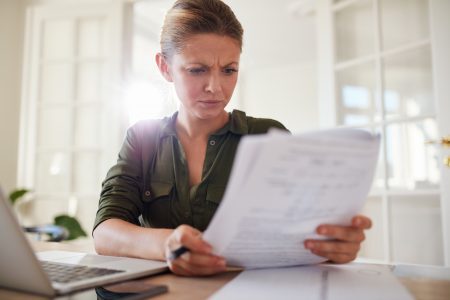
Every day, often multiple times a day, you are invited to click on links sent to you by brands, politicians, friends and strangers. You download apps on your devices. Maybe you use QR codes.
Most of these activities are secure because they come from sources that can be trusted. But sometimes criminals impersonate trustworthy sources to get you to click on a link (or download an app) that contains malware.
It has the potential to ruin relationships, reputations and our online reality. “Deepfake” artificial intelligence technology promises to create doctored…
If social media was a person, you’d probably avoid them. Facebook, Twitter and Instagram are loaded with pictures of people…
About a quarter of internet users use a virtual private network, a software setup that creates a secure, encrypted data connection between…
Instagram and Messenger are expected to inherit the end-to-end encryption their stablemate WhatsApp enjoys, but in the meantime if you’re using WhatsApp and an iDevice you can enjoy another layer of security: biometric authentication. Peeping significant others will soon need to find other ways to access bae’s messages.
Most of us will have entered into consumer contracts with large companies and ticked a box to confirm we understand…
The human brain has amazing capabilities making it in many ways more powerful than the world’s most advanced computers. So…